Digital Financial Scam | Online Banking | Job Seekers | Lucrative Employment Scam

Two Fridays back, I received a text on my WhatsApp from an international number with code ‘+213’. WhatsApp warned at the top of the chatbox, “Phone number from Algeria. Not a contact. No common groups” providing me with three options — safety tools, block, and add a contact.
The person, or potentially a bot given its system generated-like response pattern, introduced herself as Irene disguising as a hiring manager at a reputed multinational company.
Such virtual international numbers can easily be availed on the internet. I knew it’s a scam, but I decided to follow the lead to learn the modus operandi and analyse who needs to be held accountable.
Unfortunately, two of my acquaintances (on condition of anonymity) lost ten of thousands to scammers — with one losing close to NRs 190,000 and another to NRs 40,000.
They initially received payments in their eSewa digital wallet accounts thrice through different bank accounts. Afterwards, they were lured to deposit into different bank accounts scanning QRs sent by scammers, one at a time.
Scam’s modus operandi through my experience
Irene offered me a part time job where I could “earn [NRs] 5,000 and [NRs] 50,000 per day,” emphasising that the job was simple, leisurely and could be done on weekends.
I would earn NRs 600 upon completing the first assigned task and afterwards the income would depend on daily completions.
She sent me the username of a YouTube channel named ‘Traveling lord’ with a direct link to subscribe, and asked me to send her a screenshot as evidence of the job done.
I did as instructed.
Then, she asked for my personal details (such as name, age, gender, current job, eSewa QR code, and if I have a Telegram account), saying it was for “investigation record keeping.” God knows what it means.
As asked, I responded to her with a fake age and job profile.
Soon after, I received a text, asking me to redirect to Telegram and contact the receptionist named Niya (with username ‘@Runiya777’) who was assigned as my supervisor. She’d also handle any grievances including salary related that I had.
The following text said, “Send her your working code >>> Qn117-05” adding verbatim “When she back message to you, send me a screenshot please. I need to check whether you contacted person is correct or not。”
I pasted the working code in Niya’s chatbox, where she asked for my personal details again, including nationality and WhatsApp number and excluding eSewa ID.
“I’ll register it in the system so you can calculate the mission reward later,” she backed herself.
I received my first salary. My eSewa was loaded by a Siddhartha bank account.
She asked me to add her contact in Telegram so that she could invite me to join a group named ‘[212] Ordinary subscription task group’ where tasks were posted daily.
I did as said and landed at the group run by admin with username ‘@Tika2000’, who posted a total of 28 tasks — Tasks 4, 9, 14, 19 and 24 were merchant (or business) data tasks, and remaining YouTube channel subscription task or ‘ordinary task’ as they referred to it.
They would post an ordinary task every 20 minutes. For instance, 10:20 am, 10:40 am, 11:00 am and so on. However, a merchant task would be posted at 11:30 am, notifying that the next ordinary task would be posted at 12 pm.
In that half an hour interval, they would use every ethos, pathos, logos, kairos and others to persuade group members to sign up for merchant tasks with the following packages —
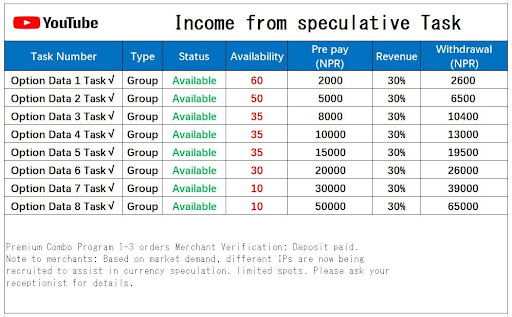
The prepayment option ranges from NRs 2,000 to NRs 50,000 with a promised return of 30% within a couple of hours.
By the time I joined the group, the clock had hit 1 pm. Out of total 28 tasks, 18 were remaining which included three merchant data tasks.
I completed the first cycle of ordinary tasks, skipping two merchant tasks. As posted in the group, I subscribed to eight well off Nepal-based YouTube channels (all having over 400k subscribers) with per task paying NRs 200.
My salary accumulated to NRs 1,600 — the minimum withdrawable amount. I received the amount in my eSewa account loaded by a NIC Asia bank account.
The channels included film production house Baasuri Films, Superhit Cinema Nepal (streaming partner of reality show Blind Date) and two individual channels — Girish Khatiwada and Aayoush Singh Thakuri.
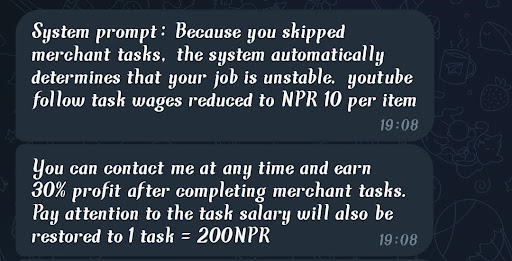
In the second cycle, I skipped the only remaining merchant task for the day. They posted usernames and links to popular channels like Mc Flo and Comedy Circle. As a punishment for skipping merchant tasks, my per task wage was reduced to NRs 10.
Niya, the supervisor, said the per task amount could be restored if I signed up for merchant tasks.
Back in the group, admin Tika announced that the group would be discontinued due to the overwhelming number of members and “continuous development of the company’s business,” asking to contact the assigned receptionist to reapply and rejoin another group.
Next day, I asked Niya about the process to apply for the merchant task. She copypasted the following from the group —
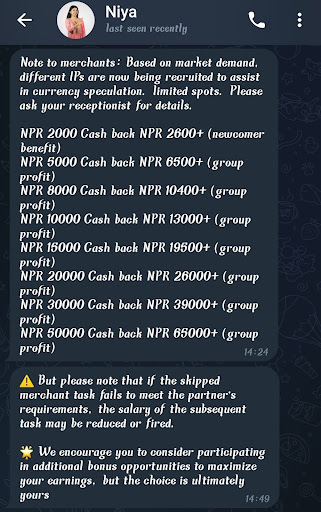
She then sent me a QR code of an account from Citizens International Bank. I averted making any payment saying my eSewa was not accepting the given QR. Upon it she strictly suggested using a mobile banking app. I haven’t replied to her since.
I reached out to several members of the Telegram group, all of whom reported that they had not fallen victim to the scam. Instead, upon receiving their first payment of NRs 600, plus an additional NRs 1,600, they immediately blocked the receptionist and left the group. The members were aware of the scam from the outset and had joined primarily to earn some quick money.
However, my acquaintances told me they were paid back with the additional 30% return and some bonus on their first merchant task of NRs 2,000. The one who lost nearly NRs 190,000 earned up to NRs 8,000 the first day.
Driven by the greed to make more out of it, they borrowed money to sign up for higher paying tasks. By the time they realised their money might not come back, it was too late.
Yet, for another two times, they believed scammers who promised them a better return with principal amount if they make one “last” deposit. In desperation to recover their original deposit for the least, they did as said. They decided not to tell their family about it, let alone filing a police complaint due to shame and stigma.
According to the Central Investigation Bureau (CIB), 4,112 incidents of cyber enabled frauds (CEF) were reported last fiscal year (2023/24). Out of which, 2,315 incidents are still under investigation, while only 25 incidents reached the court for trial.
The scammers used as many as 11 commercial and development bank accounts, and one eSewa digital wallet account to send and receive money, they revealed to me through their screenshots and bank statements.
According to a 2024 Nepal Rastra Bank report, commercial banks and development banks have reported a major portion of CEF related suspicious transactions and activities.
Scammers open accounts in multiple banks and digital wallets using the same credentials in a short period. Such credentials may be obtained from people hired as money mules.
Know-Your-Customer (KYC) of such account holders highlights they are incapable of performing frequent, and even large, digital transactions per day as seen in these accounts.
For instance, frequent debit amounts as low as NRe 1 are observed in most of the accounts reported for CEF. Such an amount is credited in various wallet accounts opened from a few common mobile numbers.
The report recommends service providers to verify the mobile number used to access mobile/internet banking and wallet accounts — whether it is registered in the customer’s own name or immediate family member name or not.
It further suggests educating account holders about safe online banking practices, and employees about cybersecurity best practices to mitigate insider threats.
A 2023 media monitoring report analysed that multiple SIM cards are issued in an individual’s name by using their personal information obtained without authority or with deceptive (uninformed) consent. Such numbers are used in opening and verifying new wallet accounts that are used in organised criminal activities, including such digital financial scam.
An additional layer in this modus operandi is scammers texting directly in numbers via SMS, adding the number in an SMS group of potential targets. The text contains job offers and a WhatsApp link leading the user to contact the hiring manager online. Like this —

How do scammers get our numbers? Do they use combination and permutation randomly or trade our data? This question leads to a broader concern — highlighting two distinct issues.
First, how secure is our data, really — all our personal information including numbers that we provide to a certain entity for a fixed purpose. For instance, providing your number (and other details) from e-commerce websites to ride sharing and digital payment apps for the purpose of opening accounts, communication, transacting and verifying our identity with sellers and logistics.
Second, how careful are we in sharing our personal information without assessing whether it’s required or not. For instance, name, number, gender, email, birthdate and location information remain with ride sharing apps.
In my media monitoring experience with Body and Data, a feminist internet/digital rights organisation, we observed different modus operandi operating throughout the year and a particular method becoming rampant in Januarys although we could not get to the bottom of this trend. Yet it appeared as if scammers went underground, studied and experimented various methods, and zeroed in on one to follow in the window of Christmas to new year month.
Read More Stories
Kathmandu’s decay: From glorious past to ominous future
Kathmandu: The legend and the legacy Legend about Kathmandus evolution holds that the...
Kathmandu - A crumbling valley!
Valleys and cities should be young, vibrant, inspiring and full of hopes with...
Understanding federal grants in fiscal federalism
Local budgets are where democracy meets the daily lives of citizensthis is a...